Tonight I was browsing the Internet, when my virus software notified me of a potential threat from openstat.ws. None of the websites open in Firefox had a link to this site in the source. After some investigation, it appears that the potentially malicious site is called by Google Adsense.
Avast Anti-virus Warning Message
I use Avast Antivirus on my computer and tonight it gave the following warning message while I was browsing the Internet:
Sign of "HTML:Iframe-inf" has been found in "http://openstat.ws/top.php\{gzip}" file
The inclusion of a URL made me suspect that one of the sites I was browsing was linking to a dodgy website (ie openstat.ws).
The obvious thing to do was to check the source of the sites open in Firefox, to see which one was the culprit. However, openstat.ws did not appear in the source of any of the pages. Not to be put off, I used the Web Developer toolbar to examine the generated source. Still nothing.
Google Says Openstat.ws Is Suspicious
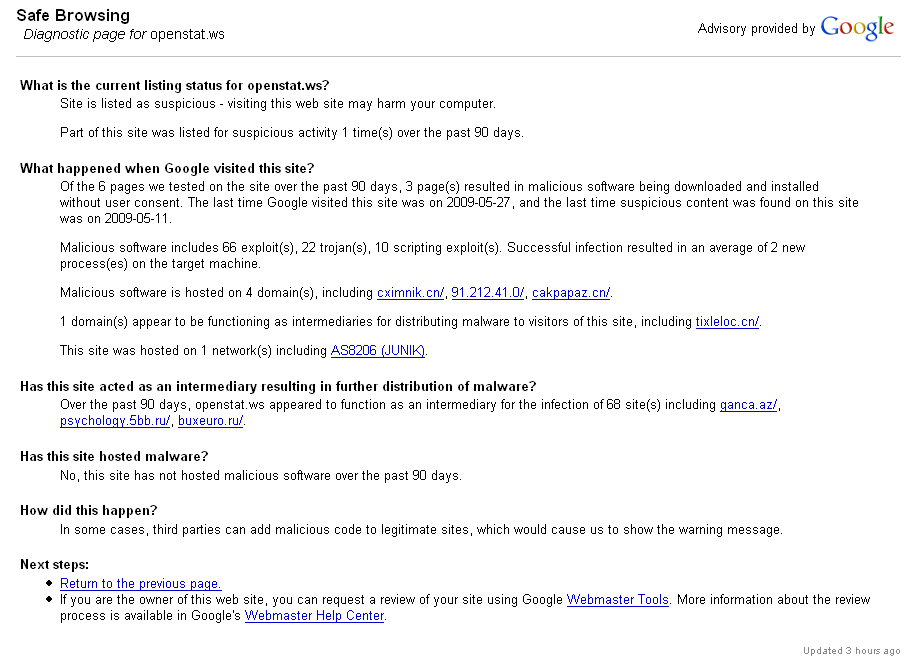
Next stop, a Google search for openstat.ws. The number one result was the Google Safe Browsing diagnostic page for openstat.ws page. Because the nature of this page is that it may change often, I’ve grabbed a screenshot of what it’s showing tonight:
Okay, so Google are saying:
Site is listed as suspicious – visiting this web site may harm your computer.
They say the site was only listed for suspicious activity once in the last 90 days, but they also say:
Of the 6 pages we tested on the site over the past 90 days, 3 page(s) resulted in malicious software being downloaded and installed without user consent.
I’m not a security expert and I may be reading this wrong (please let me know if I am), but that seems to be indicating that there’s a 50% chance of malicious software being installed from openstat.ws.
Norton Say Openstat.ws Is A Threat
The third result in the Google search was Norton Safe Web’s page on openstat.ws. Let’s see what they say about openstat.ws:
Norton are saying that there are two threats found on openstat.ws, one of which is:
Threat Name: Direct link to HTTP Malicious Toolkit Variant Activity
Location: http://openstat.ws/top.htm
The file Avast picked up on my computer is top.php, but top.htm is pretty close. HTTP Malicious Toolkit Variant Activity sounds pretty nasty. Norton say:
Severity: High
This attack could pose a serious security threat. You should take immediate action to stop any damage or prevent further damage from happening.
Okay, I’m convinced now that I don’t want openstat.ws being called on my computer. But how can I stop it where I can’t find where it’s being called from.
Looking Under Firefox’s Hood – Sessionstore.js
If openstat.ws wasn’t being called by the websites I was visiting, perhaps it was being called by Firefox itself. I started thinking that Firefox or one of the extensions I run must have been compromised. I started looking through the Firefox files – admittedly without much of an idea of what I was looking for.
I started by looking in the \Documents and Settings\[username]\ Application Data\Mozilla\Firefox\Profiles\[profilename] folder. I ordered the files in date order and started going through the most recently modified files.
I soon came to sessionstore.js. It gave me the answer, although it wasn’t the answer I was expecting. Sessionstore.js seems to store the current session, presumably so it can be restored in the case of Firefox crashing. I’m not sure if this is default behaviour or part of the Session Manager extension.
It consists of a series of entries tags, one for each tab that’s open. In examining this, I found the following:
EDIT: Due to Syntax Highlighter performance issues, I’ve moved the sessionstore.js snippet into a text file.
That’s not particularly readable, but it’s saying that I’ve got Ozh’s Handling Plugins Options in WordPress 2.8 with register_setting() post open. Inside that there is a child URL open (http://googleads.g.doubleclick.net/etc) which is a Google Adsense ad. Inside that, there are some further children, down until we come to one for http://openstat.ws/top.php, which is our suspicious site.
At this point we are still inside the Google Adsense child, meaning that the site that Google lists as suspicious is actually being served through Adsense. This is a little worrying to say the least!
Note: There is absolutely nothing wrong with Ozh’s site apart from the fact that he is running Adsense – as do I and hundreds of thousands of other sites.
Final Thoughts
As I said, I’m not a security expert, so I’d love some feedback from some more knowledgable. I’d also love to hear if anyone else out there has come across this problem.

When did this happen exactly? (GMT time)
Actually, there totally might be something wrong with my site, which would probably be more likely than Google. A site of mine has been compromised recently by some hacker who managed to find his way through an old software I wasn’t using anymore. As a result, nearly all my sites (they’re hosted off the same account) have been serving an hidden frame pulling content from a malware site. I *think* I’ve cleaned it up now, but I’m actively watching things to make sure nothing is left.
Hi Ozh,
I can’t remember the exact time, but it would have been about 11:30am GMT.
I saw Design Float was hacked the other day and they are currently serving malicious IFrames in their source. I actually looked for IFrames in your source but didn’t see any.
I don’t think the problem is with your site. Attackers could use JavaScript to inserrt malicious code in the DOM, but looking at sessionstore.js, the URL is buried deep in the Adsense ad. It’s not in your source itself.
If your site was the cause, then they must be using JavaScript to intercept Google ads, then inject the URL in those. If they’ve reached that level of sophistication, then God help us! If your site was the cause, I think it far more likely that they would have just injected something in your source.
It’s more likely that one of the advertisers that Adsense is serving up has been compromised. Or perhaps, openstat.ws is a legit site which should be served up by Adsense, but which has been hacked itself (hence it appearing as suspicious).
Anyway, if I can do anything else to help you, let me know.
FYI, I get this error message on your site, which halts the page.
“A script on this page may be busy, or it may have stopped responding. You can stop the script now, open the script in the debugger, or let the script continue.
Script: http:www.scratch99.com/wp-content/plugins/syntaxhighlighter/files/shCore.js:49”
Hi Ozh,
Thanks for letting me know. I was using the Syntax Highlighter plugin to display the snippet from sessionstore.js. The snippet was rather large and the Syntax Highlighter javascript seem to be stumbling over it (though not in Google Chrome).
I’ve now moved it into a txt file and I just link to that rather than putting the post itself.
Indeed, the “advertiser site compromised” theory sounds possible. I think by the time you paid a visit to my site, I had everything cleared. Odd stuff anyway 🙂
I’ve read about this happening quite a few times lately if you re upload the index file for the blog and or the main site it seems to fix the problem. Its also worth running a scan on your pc with combofix and malwarebytes, both of which are free but good at detecting malware not picked up by avast.
Don’t pay attention to that. Sometime virus software alarm you for nothing. They consider everything as a virus or malware. Google have no interest to take that kind of risk. They’re have a reputation to keep clean.
Its normal. People get around google protections, but sooner or later
they will be tracked and shutted down.
I wouldn’t suspect google of that. After all if something like this got into media it might mean the end of the company.
I’ve been bothered by the same alerts when I was using AVAST. But when I switched to AVG lesser alerts about this malware was popping up. If you would ignore this alert the effect of this malware will come sooner or later.
What would be its effect? This type of Malware will have an effect on your browsers. You won’t notice it but there will be times that your browser will freeze for a couple of seconds. And if this alerts keeps on coming, if your Video card or the specs of your PC cannot handle it you will encounter “Blue screen”. It is not the worst Malware but it will use some of your time waiting.
What’s the proof? It happen to me it can happen to anyone.
It should be all sorted out soon, as said above, people get around google protections, but in the end the get shut down.
That’s very interesting. Google’s own AdSense program being a culprit of suspicious malware… Doesn’t Google check the ads that are being put up through AdWords? I mean, I guess not seeing from this result. However, you would still think this is something Google would check for..
Thanks for the informing post, I’ll be sure to look out for this.
Hard to say Jesse – you would think that they would check, but they must be serving up an insane number of ads from huge number of advertisers…
Malware, Google not often seen in the same sentence. I would suggest it is down to the sheer volume they are churning out daily. Surely they can keep an eye on every one.
Man, I sure would want some updated information about this. Adsense?!
Thing, however, is that I haven’t heard of any more of this besides Ozh’s.
I’m sorry for my comment.
Just in my opinion, what about the chance that the anti virus have some bug?
Very complete post. About a month ago, my Kaspersky antivirus told me the Google ads are infected. I supposed it’s a bub of Kaspersky. However, if google wants to spy you it’s very easy with some cookies I supposed.